From Shadow IT to Shadow AI - we cover your stack!
Discover and secure your growing application attack surface, including SaaS, internal apps, AI-driven, and agentic AI, by eliminating misconfigurations, reducing exposure, and responding to threats in real time.

Security teams globally choose Wing





















SaaS and AI are the new attack surface… and it’s exploding.
Unmanaged apps. Dormant accounts. Forgotten admin access.
All offering attackers more ways in – hidden in plain sight.
Too Many Apps
Connected tools, shadow integrations, and OAuth sprawl under the radar.
Too Much Access
Employees, service accounts, and vendors with stale or dangerous privileges.
Too Little Control
Risk scores without context, endless alerts, and complex tools without effective action.
WING SECURITY PLATFORM
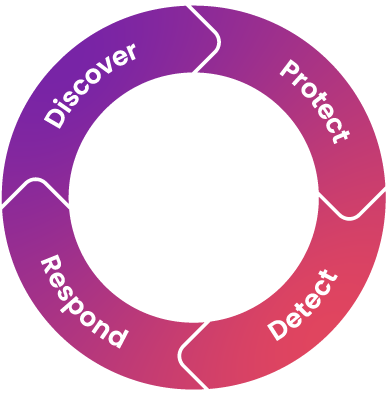
Protecting the application attack surface requires a holistic approach
Wing applies a continuous, holistic approach to secure the application attack surface – discovering shadow IT and AI, detecting vulnerabilities, and tracking identities, privileges, and behaviors across your stack.
Critical exposures like dormant super admins, overprivileged tokens, and abnormal activity are surfaced and prioritized to help security teams act fast.

SEE YOUR STACK
Discover your blind spots
Uncover your entire stack – SaaS, Internal apps, AI-driven and Agentic AI in minutes and expose security gaps like misconfigurations, over-privileged AI agents, stale users, and more.
MANAGE EXPOSURE
Fix what matters, meet compliance requirements
Mitigate risky misconfigurations and access privileges fast, reduce your attack surface and demonstrate compliance with key frameworks.
DETECT THREATS
Respond with confidence
Stay ahead of attackers with real-time detection and response. Seamlessly integrate with your existing SIEM and SOAR tools to orchestrate complex workflows.

Talk with a Wing Security expert
Let’s have a quick chat and show you Wing in action.


Uncover Shadow IT. Govern Shadow AI. Protect the Enterprise.
Understand and strengthen your security posture with full visibility into your entire stack, including hidden risks across your SaaS and internal apps, AI agents, Agentic AI, and every identity – human or not.
Discover Shadow IT
Gain awareness and deep context into your Shadow SaaS and internal apps, uncover unsanctioned apps, usage patterns, and associated risks across your environment.

Detect Shadow AI
Prevent unmanaged risks, ensure data security, and maintain control over how AI, including GenAI apps, AI agents and agentic AI, is used across your organization.

Access Control and Governance
Ensure that users, both human and non-human, have only the access they need, enforce Zero Trust and least privilege principles by continuously identifying and removing excessive or unused access.

Supply Chain Risks
Control threats introduced by third-party vendors that have access to your systems, data, or infrastructure, and apply strong security controls across all external dependencies.

Audit and Compliance
Meet compliance standards like SOC 2 and ISO 27001 by providing visibility into your application security posture and ensuring accurate, ongoing assessments of third-party vendors.

Resources
What our customers are saying

Talk with a Wing Security expert
Let’s have a quick chat and show you Wing in action.





